By
Keeta Team
The Compliance Wall That Blocked Blockchain From Banking
Why traditional blockchains are difficult for banks to adopt and how Keeta addresses those constraints at the protocol level.

As of today, not a single major bank in the world runs a public blockchain as its core financial infrastructure. It is not “technophobia”, it is the result of a very specific collision between what blockchain was designed to do and what banks are legally required to do, and those two things have been fundamentally incompatible for the better part of two decades.
It starts with understanding what banks are legally required to know about every transaction they process.
What Banks Are Required to Know
Before we get into blockchain, it is important to understand the legal ground banks stand on. Banks are not free to process money however they see fit. Every regulated financial institution in the world operates under a framework of laws designed to prevent money laundering, terrorist financing, and the movement of funds tied to criminal activity.
The most important of these is something called the Travel Rule.
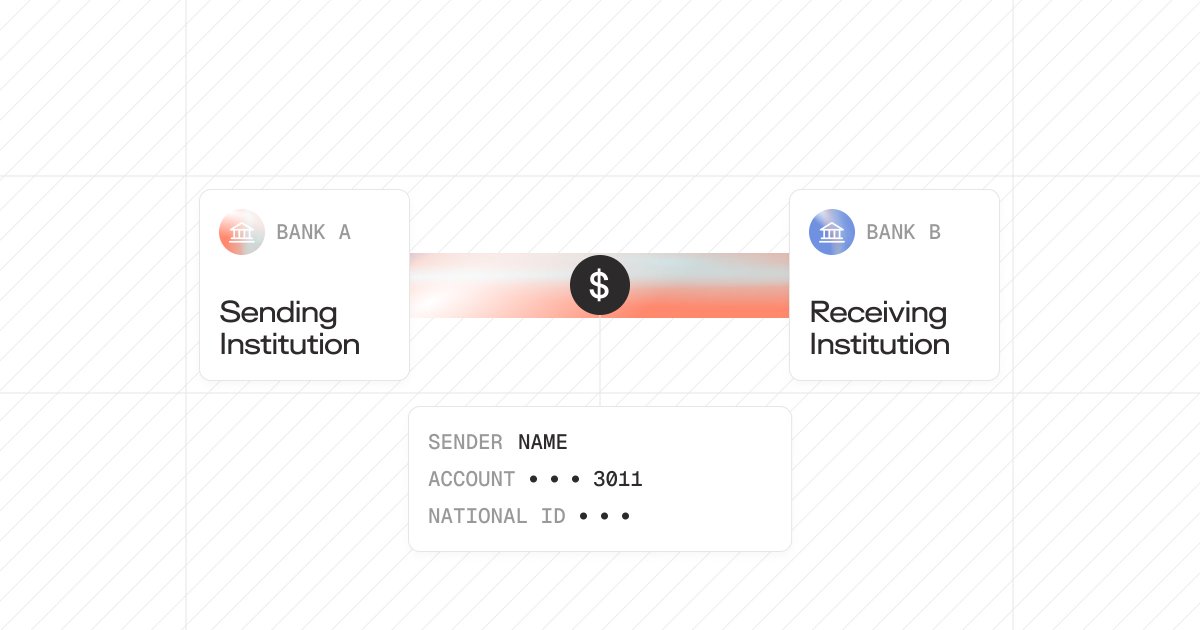
The Travel Rule was originally established in the United States under the Bank Secrecy Act in 1996. Its job is straightforward: when money moves between financial institutions, information about who is sending it and who is receiving it must travel with that money.
The institution sending the funds is legally obligated to collect the sender's name, account information, and, in many cases, a national identification number. That information must be passed to the receiving institution before or during the transfer.
If a bank is involved in moving your money, it must be able to answer, with documented evidence, two questions:
Who sent this? Who received it?
What Blockchain Was Built to Avoid
Public blockchains - Bitcoin, Ethereum, and the vast majority of networks built over the last 17 years - were designed explicitly to enable transactions without a central authority needing to know who you are. One of the foundational philosophies of decentralized cryptocurrency was financial independence: the ability to move value without asking anyone for permission and without revealing your identity to any institution.
On Bitcoin or Ethereum, you are represented by a wallet address, essentially a string of letters and numbers. The address is public. The balance is public. Every transaction you have ever made from that address is permanently recorded and visible to anyone in the world with an internet connection. But the address itself is not tied to a name, a passport, a national ID, or any verified identity. You are effectively anonymous.
This works beautifully if your goal is censorship-resistant peer-to-peer transactions. It is a complete no-go for any regulated bank or other institution, however, for a simple reason: a bank that processes a transaction without knowing who sent it and who received it violates federal law.
The Second Problem: Too Much Transparency
Anonymity is the first compliance wall. But banks face a second problem that is equally disqualifying, and it pulls in the opposite direction.
Public blockchains like Bitcoin and Ethereum are completely transparent. Every transaction, every balance, every movement of funds is permanently visible to anyone. While this creates challenges for individual privacy, it creates a different and equally serious problem for institutional finance.
A bank cannot have its entire transaction flow visible to competitors, counterparties, and the public. If every payment a bank processed, every institutional trade, every payroll movement, and every treasury operation were publicly readable on a ledger, the bank would be handing its competitors and bad actors a real-time view of its entire business.
As TRM Labs notes in their 2026 research paper on on-chain privacy and financial compliance:
“Businesses cannot conduct payroll, vendor payments, or treasury operations on systems where competitors can observe every transaction. Market makers and institutional traders cannot operate where their positions and order flow are publicly visible.”
Public blockchains, therefore, present banks with an impossible choice: either accept the anonymity of addresses (which violates AML law), or accept the full public transparency of the ledger, which makes operating commercially untenable. Neither option is workable, and no amount of speed or cost efficiency changes that calculation.
(Source: TRM Labs, "On-Chain Privacy and Financial Compliance," 2026; OMFIF, "Scaling Trust With Blockchain Infrastructure," 2025)
Why Workarounds Did Not Work
The blockchain industry has spent years attempting to solve the compliance problem by adding layers on top of existing networks rather than building compliance into the foundation.
Banks, recognizing early that public chains were unusable for regulated activity, tried a different approach entirely. Rather than working with public blockchains, they began building their own — private, permissioned networks where access was restricted to approved participants and every user on the network was known. JP Morgan built Quorum in 2016, a private version of Ethereum that only authorized counterparties could access. The logic made sense at the time: if you control who is on the network, you control who is transacting, and the anonymity problem disappears.
The problem was that this approach solved one issue while creating several new ones.
Each institution that built a private chain built it to its own standards, different data formats, different consensus mechanisms, and different compliance logic. When those institutions needed to transact with each other, which is the entire point of a payment network, there was no common infrastructure layer connecting them.
A tokenized asset issued on JP Morgan's private ledger could not move freely to a counterparty operating on a different institution's private chain. Settlement still required intermediaries. The inefficiency of the existing system was largely preserved, just dressed in different technology.
As Chainlink's enterprise research noted, the era of private institutional blockchain adoption produced significant liquidity fragmentation - where assets and capital became effectively trapped within individual networks, unable to move freely across the financial system. A tokenized asset confined to one institution's ledger is, in practical terms, not much more useful than a record in a spreadsheet.
The compliance problem was never solved. It was deferred, patched, and the fragmentation it produced became a problem in its own right. What the industry needed was not a private chain for each institution or a compliance layer bolted onto a public one. It needed a network where compliance was structural - built into how the protocol itself operates from the ground up.
(Sources: Chainlink, "Private Blockchain Interoperability: Connecting Enterprise Chains")
The Network That Was Built To Solve This
Keeta approached this differently. Rather than building a blockchain first and then attempting to make it compliant, Keeta built compliance into the protocol's architecture from the beginning.
The mechanism that makes this possible is a system of X.509 certificates attached to accounts on the network.
X.509 is not a new technology. It is the same certificate standard that underpins TLS encryption - the technology that secures HTTPS connections across the internet. It is a globally recognized, institutionally trusted format for verifying identity. Keeta uses it as the foundation for how identity is handled on the network.
A user who needs to be verified, for example, to meet the requirements of a regulated financial institution, gets verified by a Certificate Provider. This could be a government agency, a regulated financial institution, a KYC provider like Footprint, or any trusted entity with the authority to issue that type of credential. The Certificate Provider issues an X.509 certificate that attests to the user's verified identity. That certificate is attached to the user's account on the network.
No personally identifiable information is stored on the ledger itself. The certificate confirms that identity has been verified, and by whom, without publishing the underlying data - your name, address, passport number to the world.
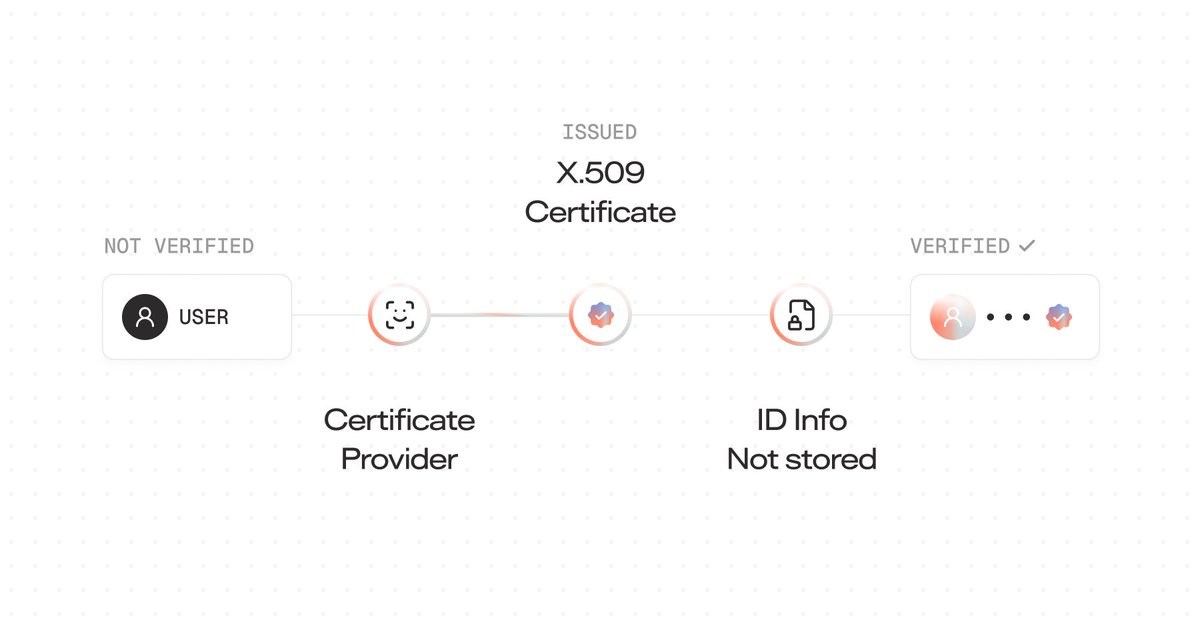
When a counterparty receives a payment from your account, they do not see your personal information. They see that your account has been certified by a trusted institution and that the transaction is therefore compliant.
This makes Keeta the first blockchain network in the industry with native compliance with the Travel Rule built directly into the protocol.
KYC Is Optional - By Design
One of the most important design decisions Keeta made is that KYC is not mandatory by default across the network. It is a capability, not a requirement imposed on every user regardless of context.
Accounts on Keeta do not carry certificates unless a certificate is required for a specific interaction. If a user wants to transact anonymously within the boundaries of what the network and applicable law permit, that is supported.
A user without a KYC certificate can still participate in the network; they simply cannot access services or counterparties that require verified identity, the same way a person without a bank account cannot access services that require one.
Compliance That Enforces Itself
Identity verification solves one half of the compliance problem. The other half is control - and control, in traditional finance, is almost entirely manual.
A bank that issues a restricted financial product today has to build or license a separate system to enforce who can hold it, who can receive transfers from it, and under what conditions those transfers can happen. When regulations change, that system has to be updated manually. When a transaction breaches a rule, a human has to manually catch it. The compliance layer and the transaction layer are two independent things that have to work together, and the gap between them is where failures happen.
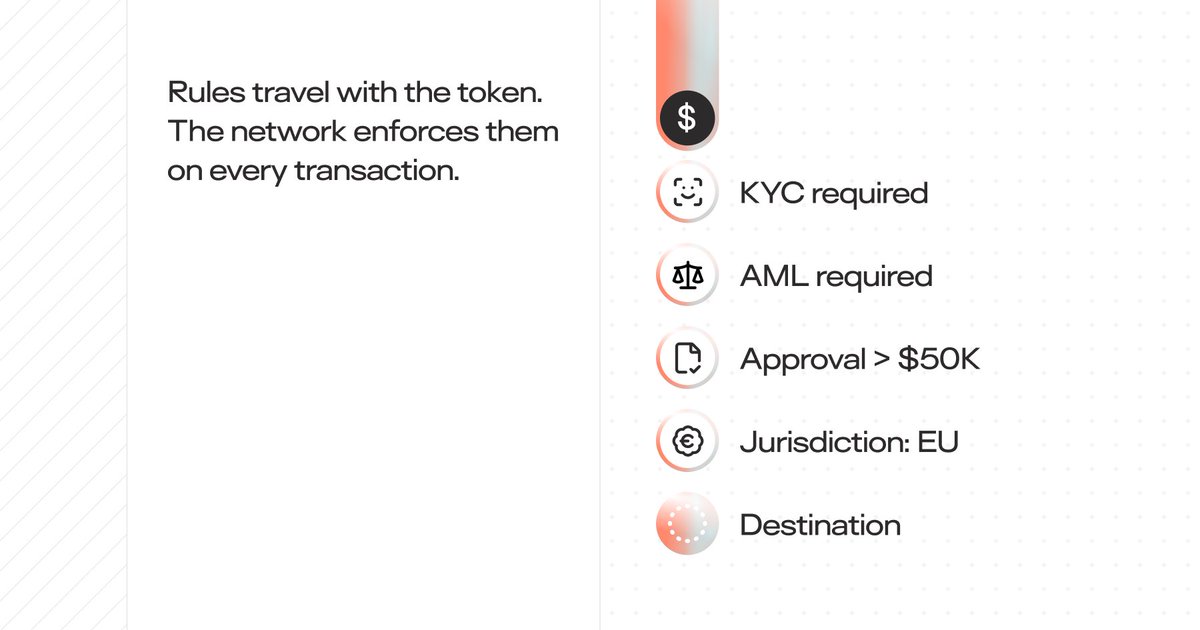
Keeta removes that gap entirely through its built-in rules engine - a system that allows compliance logic to be attached directly to tokens at the point of issuance and enforced automatically by the network on every transaction, without any manual intervention required.
The way it works is straightforward. When a token is created on Keeta - whether that is a tokenized currency, a financial product, or any other asset - the issuer can define a set of rules that govern exactly how that token can be used. Those rules travel with the token. These rules are enforced at the protocol level, meaning there are no underlying smart contracts, which are separate pieces of code that sit on top of the network and can contain bugs, be exploited, or be deliberately written with backdoors.
To understand what this means in practice, here are a few examples:
KYC-Enforced transfers only: An institution issuing a regulated financial product can set a rule that restricts transfers exclusively to accounts that hold a valid KYC certificate. If a wallet without a verified certificate attempts to receive the token, the network blocks the transaction before it processes.
Jurisdiction enforcement: A token can be programmed to only transfer between users in approved jurisdictions. If a financial product is authorized for EU residents only, the rule engine checks the recipient's location against that restriction during each transaction. A recipient outside the approved region cannot receive the token, regardless of any other factor. This means a bank issuing a product that is compliant in Germany but not in Singapore does not need a separate enforcement mechanism for each market - the rule is embedded in the token and enforced identically everywhere the network operates.
Approval requirements: For high-value or sensitive transactions, a rule can be set requiring that a designated administrator review and approve the transfer before it can proceed. A transaction above a certain threshold does not settle automatically - it enters a pending state and cannot move until the approval condition is met. This mirrors the internal controls that banks apply to large transfers today, except that the control is built into the protocol rather than sitting in a separate system that can be bypassed or misconfigured.
Time locks: Tokens can be programmed so that they cannot be transferred or used until a specific date or condition is met. This has direct applications in vesting schedules and escrow arrangements, to name a couple. On Keeta, the lock is enforced by the network itself, at the protocol level, and cannot be circumvented.
One of the most important properties of the rules engine is that it is updatable after issuance. Regulations change. Market conditions change. A rule that is compliant today may need to be revised when new legislation takes effect. On Keeta, token issuers can update the rules attached to a token at any point, and those updated conditions apply to all future transactions involving that token from the moment the change is made. An institution does not need to recall and reissue a token every time the regulatory environment shifts - they update the rule, and the network enforces the new version going forward.
How Keeta Enforces Private Transactions
One of the biggest issues that kept banks away from public blockchain infrastructure was the fully transparent ledger. When every transaction is permanently visible to anyone who looks, operating becomes commercially untenable for any institution moving serious capital.
A bank cannot broadcast its payment flows, counterparty relationships, and treasury movements to the public in real time.
Keeta addresses this through a layered approach to transaction privacy, the most significant of which is its support for private subnets.
A subnet on Keeta is a separate, independently operating network that runs on the same underlying protocol as the main Keeta network but with its own rules, its own participants, and its own visibility controls. You could think of it as a gated section of the network where participation and visibility are restricted to approved parties. The important distinction is that a private subnet and the public Keeta mainnet are connectable. A bank operating on a private subnet can still settle against the public ledger, access liquidity from the broader network, and interact with participants outside the subnet when needed.
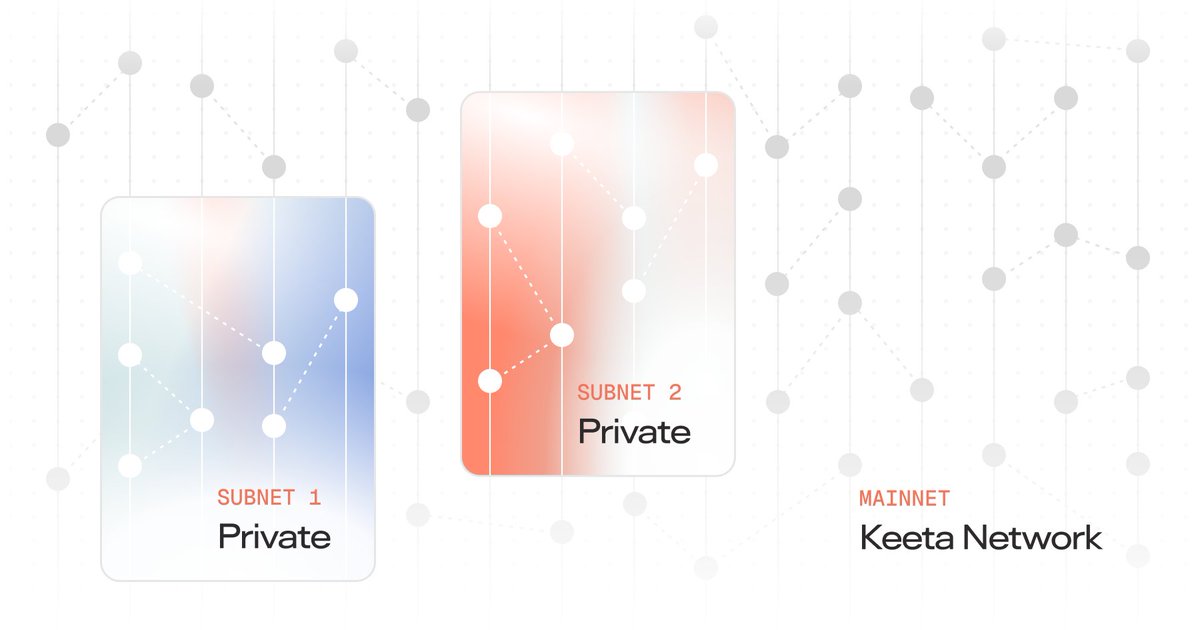
Subnets are not the only privacy mechanism, and the protocol was not designed around a single privacy method, leaving room for other implementations.
The Infrastructure That Was Actually Missing
For 17 years, the blockchain industry tried to push banks toward a model that was fundamentally incompatible with the legal frameworks they operate under. It asked regulated institutions to do the impossible: process transactions without knowing the sender, on a ledger visible to the entire world.
Keeta solves both sides of the equation. Identity is verifiable without being publicly exposed. Compliance is built in, not bolted on. Privacy is preserved through selective disclosure rather than stripped away. And the system is flexible enough to accommodate both fully private peer-to-peer transactions and fully compliant institutional financial operations within the same network.
The compliance barrier that kept blockchain out of banking for 17 years has finally been broken, and it starts with Keeta.

